e
q
u
e
s
t
a
d
e
m
o < back
HUSH HUSH MASKING SSIS COMPONENTS MANUAL
Hush Hush is a collection of SSIS data flow transfo
rmationtransformation components that encapsulate entities
and their rules of generation, with the exception b
eingbeing Generic Alpha Numeric component.
The components expect
string type
data on input and provide
string type
data on output.
HUSH HUSH MASKING SSIS COMPONENTS MANUAL
Hush Hush is a collection of SSIS data flow transfo
rmationtransformation components that encapsulate entities
and their rules of generation, with the exception b
eingbeing Generic Alpha Numeric component.
The components expect
string type
data on input and provide
string type
data on output.
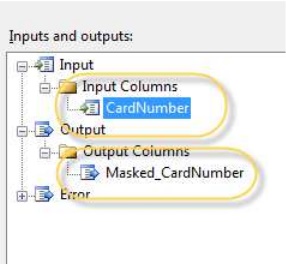
Every component allows for one field only on input.
It creates another field that has the masked
value in it. The name of the new column is a concat
enationconcatenation of the word “Masked”, underscore
and input field’s name.
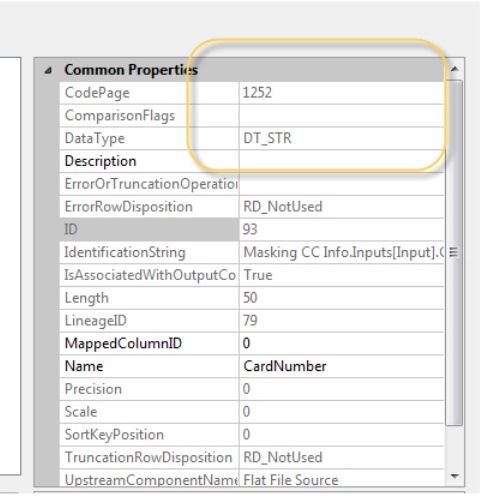
Each component is strongly typed. It expects specif
icspecific types of data. Upon input, it will confirm
data type and rules of formation. Without this info
rmation,information, the component will fail. Three types
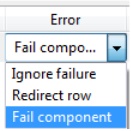
error handling allow for “fail component”, “redirec
t“redirect row”, and “ignore failure”.
Components employ two major algorithms. One allows
for the random substitution of values.
The other utilizes proprietary encryption–like algo
rithms.algorithms. Both components use entity type in a
title. The later ones have the word “Dynamic” in th
ethe title.
Random components replace data in a truly random fa
shion.fashion. Values don’t’ get bound to original
values; they can also repeat. The randomness introd
ucesintroduces the danger of inconsistency among the
masked data comparing to original. In order to main
tainmaintain referential integrity and -when necessary
-uniqueness as it is often a case with SSN or credi
tcredit card numbers, one has to create additional
structures, so-called mapping tables. One has to in
sureinsure that corresponding values are mapped
into the table without duplication. There are sever
alseveral ways to achieve this, methods include using
distinct clauses at the source, the use of unique i
ndexes and simply by looking up components of
SSIS.
Dynamic components retain referential integrity wit
houtwithout any additional structures. However, by
the nature of encryption, there is a possibility of
decryption by unauthorized parties. Therefore,
the decision is up to the practitioner on whether t
oto use the “Dynamic” or the
“Random”component. Some of the components (with a l
esserlesser security threat) at this time only
provide the encrypted algorithm. Newer versions wil
lwill have random algorithms for entities as
well.
Only Social Security Numbers, Credit Card numbers, US Phone numbers, and Phone Numbers guarantee that unique data sets will map to a corre sponding, unique data set. Names, Address elements, components, URLs, Dates of Birth and Zip Codes do not guarantee unique data set on output but provide sufficient amounts of output val ues to test upon for various KPIs.
